When you live in the world of AIOps, it’s easy to focus on technology. Whiz-bang stuff like artificial intelligence and advanced analytics driven by machine learning algorithms is impressive, but whether it’s a rock strapped to a stick or a sophisticated software platform that lives in the cloud, technology is a tool. And tools are only worthwhile if they help you get a task done quicker and easier than the way you did it before.
For those involved in IT operations management (ITOM), that means your tools have to be good at IT event management and incident management. ITOM is, after all, about the management of IT. And in order to properly manage IT, you have to be able to monitor and manage the processes performed and supported by the technologies that comprise your IT estate. That means you’ve got to manage events, anomalies, incidents, CMDBs, and all the data that flows to and from devices and services. Let’s take a closer look at these things to better understand what they are and why they are important.
What is IT event management?
In IT operations, an event is any detectable or discernable occurrence that has significance for the management of the IT infrastructure or the delivery of IT service and evaluation of the impact a deviation might cause to the services. Events can be warnings and exceptions generated by the software based on user actions (clicking on a link with your mouse), or system occurrences (running out of memory). Software can also trigger its own set of events to communicate the completion of a task. There are three primary categories of events.
- An informational event is a type of event is used to check the status of a device or services to confirm it’s working and capture statistics for determining patterns of behavior. Like heartbeats, informational events happen because your infrastructure is working, and data is being generated and moved through your network.
- Warning events are generated when a device or service is approaching some pre-defined threshold. Warnings are intended to notify the operations people/processes/tools so they can proactively take any necessary actions to prevent an exception.
- Exception events indicate that a service or device is currently operating outside the ‘normal’ or ‘expected’ parameters (thresholds). This means that the business service is impacted and the device or service displays a failure (fault), performance degradation, or loss of functionality (server down, insufficient disk space, slow response time).
IT event management is a way of monitoring all events that occur through the IT infrastructure. It allows for normal operation and also detects and escalates exception conditions. Like an EKG machine, you listen for the pulse, but sometimes detrimental situations happen. When they do, an event may be classified as a warning or exception that in turn, generates an incident.
What is IT incident management?
IT events that are “unexpected” (warnings or exceptions) and anomalies may trigger a response known as an incident. IT incident management is a process that focuses on returning the performance of an organization’s services to normal as quickly as possible, minimizing the impact on business operations. Sometimes incidents are harmless and reflect a temporary, self-correcting situation; other times they can mean trouble—either that a failure has occurred, or that there is a situation imminent that could lead to a failure if not corrected.
Through IT incident management, the organization can affect a rapid and informed response to ensure resolution of whatever problem is occurring or about to occur, and a restoral of operations to the best possible levels of service quality and availability.
What are anomalies?
Anomalies are weird behaviors, and like events, not all anomalies are bad. Anomalies are different because they are not pre-defined but are generated by artificial intelligence (AI) and machine learning (ML) to reflect changes in behavior that may or may not be outside the thresholds of ‘normal’ or ‘expected’ behavior. For example, your heart rate flatlining at 60 may simply mean that you are resting. But if you investigate it as normal behavior, your heart rate would likely fluctuate slightly.
Unlike anomalies, incidents bear closer inspection and may require corrective action.
What is the difference between IT event management and IT incident management?
It’s important to recognize the difference between IT event management and IT incident management because they are not the same thing. IT event management is a largely passive process that knows what is expected of the systems and services operating within the enterprise, makes sure they function properly and records all events and their associated data. IT incident management is an active process that happens when things go wrong. For IT incident management to be effective, it is vital to know not only what the expected action is, but also as much detail about the conditions surrounding the unexpected incident as possible in order to inform corrective action.
What is event correlation?
Nowadays, when discussing IT event management it’s also important to mention event correlation. Event correlation is the technique of gleaning context from a large number of events and pinpointing what events are important and what is noise. The secret to getting the context you need to correlate events is service topology. Service topology helps determine if the event is a casual event versus a symptomatic event. Example: You may get hot and/or sweaty when your pulse quickens, but your body temperature is a symptom—not the cause. The cause is your heart.
What is the IT event management lifecycle?
Because IT event management is a process, there are steps that must be taken to ensure it happens properly. These steps constitute the IT event management lifecycle, and they are:
- Occurrence: An event takes place within the enterprise IT estate;
- Detection: The event that occurs is detected by the enterprise’s IT monitoring tool;
- Record: A record of the event is made in the system log;
- Notification: IT management is notified of the event
- Correlation: The event is analyzed within the context of all relevant data to determine if the event falls within expected parameters, or if it should be classified as an incident requiring corrective action. Modern correlation doesn’t just consider events but also considers ML-driven anomalies within a service context.
- Response: If an event is informational or symptomatic (not causal but related to another event), it is recorded as such. If an event is “causal” and treated as an incident, machine or human intervention is triggered to fix the problem; Anomalies can contribute additional meaningful context to an incident.
- Closure: Upon completion of the appropriate response, any actions are once again logged, the incident is updated and closed, the event is updated and closed, and the lifecycle continues.
What is the role of a CMDB in IT event management?
An enterprise’s configuration management database (CMDB) is a database used to store information about an enterprise’s hardware and software assets and is the “heart” of the IT estate’s service management system. When a configuration item (CI) is added or changes state, it is recorded in the CMDB. Critical information about the CI is stored in the CMDB to track the owner, maintenance schedules, support information, and more. This information is used to ensure optimal incident management.
Nothing exists within the enterprise without affecting CIs both upstream and downstream. When properly populated and maintained, the CMDB provides a complete, accurate, view of the enterprise in real-time. That requires inputs that can be trusted to provide real-time updates to the CMDB. When the CMDB is up to date, it ensures reporting of contexts necessary for proper IT event management and IT incident management.
Why is clean data essential for effective IT event management?
The old saying, “Garbage in, garbage out” is true for maintaining a CMDB, and for effective IT event management and IT incident management. Clean data is more than just accurate data; clean data has to be complete and timely. Achieving clean data requires real-time discovery of the entire IT estate, the elimination of operational siloes, and the normalization and storage of data in a single operational data lake.
Clean data can be used to provide context for IT event management and IT incident management decisions, for enriching IT incident management tickets, deriving meaningful insights through analytics, and for establishing an IT operations management strategy that is best suited to supporting your organization’s business or mission objectives.
What are the primary challenges to IT event management?
The first and possibly biggest challenge to maintaining an effective IT event management process is achieving complete, real-time visibility across your entire IT estate. That includes the discovery of CIs that are on-premises and in the cloud; physical and virtual; permanent and transitory.
A device that is operating and drawing resources from your network that is unaccounted for could have a negative effect on IT event management because its operation may deprive IT operations monitoring and management tools of proper context. The same with a computing instance that may be online for a short while and then shut down. That CI may have affected data and operations for as long as it was running, but with no record of its existence or how it relates to other devices, that data lacks necessary context.
Another major challenge to IT event management is the establishment of an operational data lake filled with normalized data. If IT operations is drawing on different sources of non-normalized data, there will be no way to account for contextual relationships, duplicated data, or reconciling different formats to ensure consistent results.
The third major challenge of IT event management is the overwhelming noise that occurs when you gather data from across your entire IT estate. The sheer volume, variety, and velocity of data – logs, metrics, events, anomalies, topology – generated from your IT systems is well beyond traditional human analysis and response.
How can you overcome IT event and incident management challenges?
The best way to overcome the challenges to effective IT event management and incident management is to build from a platform that is engineered to support the full scope of technologies present in a modern enterprise, including legacy systems, hardware, and software-based systems, on-premises and cloud-based assets, and whatever systems your ongoing digital journey may require.
This platform should support real-time discovery across traditional and hybrid infrastructures, take advantage of artificial intelligence and machine learning to enable real-time operations and analytics, and be able to create, populate, and manage an operational data lake filled with trusted data. The platform must add critical context to the data and apply analytics consistently across ALL the contextualized data to eliminate the noise and accelerate root cause analysis. Finally, the platform must be capable of building and supporting intelligent automations to ensure the enterprise is functioning as efficiently and reliably as possible, tackling repetitive tasks in order to liberate skilled employees for higher-level operations and innovations.
That’s an ambitious wish list, but the ScienceLogic SL1 platform satisfies all these demands. SL1 has become the unified platform of choice for forward-thinking organizations that want to make the most of their IT investments, and that have a vision for the future of IT operations that is not constrained by the limitations of legacy ITOps technologies.
Ready to learn more about what ScienceLogic can do for you? Read this eBook>
 See ScienceLogic in actionTake a Tour
See ScienceLogic in actionTake a Tour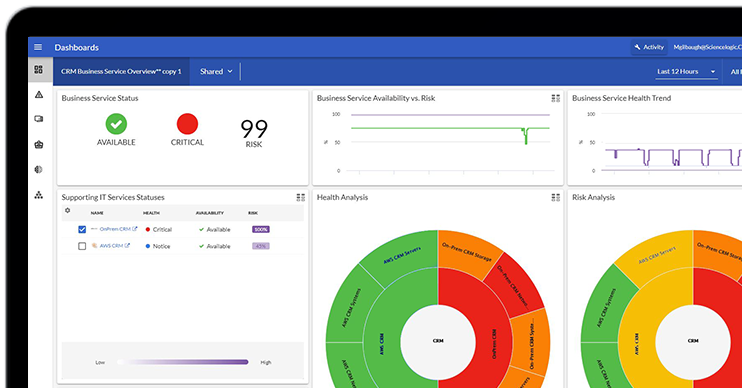 Take Skylar One for a SpinStart Your Test Drive
Take Skylar One for a SpinStart Your Test Drive The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report
The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report
The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report Become a PowerPack PicassoRegister Today
Become a PowerPack PicassoRegister Today
