What is SecOps?
Security operations, or SecOps, is an approach to enterprise IT management that facilitates collaboration between an organization’s IT operations and IT security teams. SecOps recognizes that the security of an enterprise is enhanced when infrastructure is operating at peak efficiency, systems are discovered and monitored in real-time, and all data related to IT operations is accurate.
Today’s enterprises are highly complex, fast-moving, and continuously changing state. If IT operations are not managed well, it is easier for threat actors to attack and compromise systems within the environment without raising suspicion. One recent report found that 54% of enterprises cited lack of infrastructure visibility as a primary challenge for security. When SecOps teams have a complete view of an organization’s infrastructure, including hardware, software, virtual systems, services, and applications, it’s easier to see and respond to events and incidents that may be indicators of compromise (IoC).
SecOps Benefits & Goals
Threat actors are excellent at finding and exploiting weaknesses in a network environment. The onset of the COVID-19 pandemic and resulting sudden shift to remote work has exacerbated that fact. Many organizations rushed to accommodate remote work without taking proper security precautions. As a result, VPN attacks have risen nearly 60 percent, while the instances of security incidents due to cloud configuration errors is up nearly 20 points since early 2020.
Whether it is an edge device with a weak or default password, a misconfigured cloud service, or an unprotected mobile device that has connected to the network outside of the view of IT operations, IT security can’t close security gaps or respond to IoCs if it is not aware of them. That is where SecOps comes into play.
The goal of SecOps is to gain a complete, contextual understanding of an organization’s infrastructure to keep systems and users safe. By aligning IT ops and security, SecOps can achieve the visibility it needs to keep systems and data secure, reduce an organization’s risk profile, and also have the information and insights needed to support the overall health, availability, and reliability of the enterprise.
With IT operations and security teams properly aligned, SecOps delivers key benefits to the enterprise, including:
- Identification and mitigation of cloud and application configuration errors;
- Implementation of process automation to minimize manual/human errors;
- Enforcement of regulatory, security, and IT policy process compliance;
- Pre-deployment confirmation support for DevOps; and,
- Efficient patch management.
Common SecOps Tools
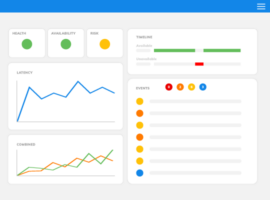
Because the goal of SecOps is to maximize enterprise security, many tools of the SecOps trade are familiar to IT security professionals. They include things like firewalls and perimeter defenses, intrusion detection, vulnerability scanners, network monitors, and encryption. For those with a background in IT operations they may be more accustomed to tools like IT operations monitoring and management platforms, workflow and service management software, application and network monitoring systems, and analytics.
Where SecOps earns its keep, however, is in using the insights gained from the IT operations side to inform action on the security side. The complexity of today’s enterprises requires machine speed and intelligence to make the best decisions in real-time.
Whether it is the encryption of transferred files, segmentation of non-secure devices deployed to the network edge, or rigid adherence to application testing and deployment policies, automation and orchestration can bring order to the chaos that characterizes IT operations—and that threat actors count on for their success.
As such, tools that emphasize and enable automation and orchestration are key. This is important to ensure compliance at all levels of operations. Some of these tools include:
- Security Information and Event Management (SIEM);
- Artificial Intelligence for IT Operations (AIOps);
- Security Configuration Management (SCM);
- IT Operations Management (ITOM);
- The MITRE ATT&CK Framework;
- Threat Intelligence Services; and,
- DevOps tools and processes.
SecOps Best Practices
As with improving network operations, the first step in achieving SecOps success is in tearing down operational silos. No more turf battles or finger-pointing. IT operations and security teams have to work together as one, with seamless communications and a common goal.
Any change to organizational culture presents a challenge, but for SecOps the journey begins with leadership coming together to establish a common vision and set organization-specific goals that can unify all involved while supporting both IT operations and security. When each element of the SecOps organization recognizes how it complements the other—and when the promise of mutual success is demonstrated by results—the task becomes easier.
Investing in the right tools and processes is important for building a successful SecOps team, but it is the people who use the tools that have to be convinced. Applying the crawl-walk-run approach to implementation and momentum building is important for setting reasonable goals, cultivating champions, and avoiding discouragement.
The Future of SecOps
IT operations and security can no longer exist as separate entities for today’s modern enterprises to succeed. A SecOps approach to enterprise IT management is needed to ensure an organization’s tech infrastructure is both secure and functioning at maximal efficiency. Threats like malware, ransomware, crypto mining, and others present a serious risk to business operations, denying users and customers access to the resources they need to be productive and successful.
Cyberattacks like those that struck Colonial Pipeline, or that exploited digital supply chain vulnerabilities through the SolarWinds IT software management attack, stand as a stark reminder of the ever-present dangers facing today’s enterprises. You don’t have to be a Nobel Prize-winning genius to understand this simple fact: organizations that fail to recognize that IT operations and security must work together needlessly put themselves and their employees, as well as their customers and trading partners, at risk of a potentially crippling attack.
Innovations in both technology and the ways in which organizations manage their IT operations can help minimize threats. SecOps is an innovation that can make the most of the many tools that are available to the modern enterprise.
Learn more about ScienceLogic and SecOps>
 See ScienceLogic in actionTake a Tour
See ScienceLogic in actionTake a Tour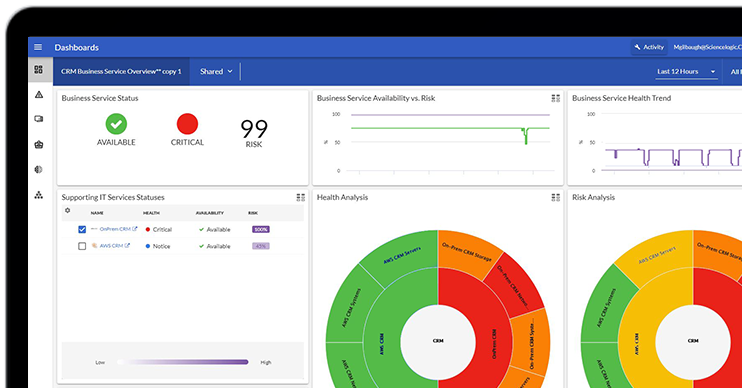 Take Skylar One for a SpinStart Your Test Drive
Take Skylar One for a SpinStart Your Test Drive The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report
The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report
The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report Become a PowerPack PicassoRegister Today
Become a PowerPack PicassoRegister Today