Entertainer Jim Stafford had a hit song in 1974 entitled “Spiders and Snakes.” I was thinking that would be a good song to put on a playlist for the ScienceLogic crew that takes the road trip to the Department of Defense Test Integration Center (TIC) in Fort Huachuca, located in the desert of southeast Arizona.
Fort Huachuca is an appropriate place for technologies to be tested as part of the Department of Defense Information Network (DoDIN) approved products list (APL) process. The environs in and around the fort, about ninety minutes southeast of Tucson, are not especially welcoming. It is hot and dry most of the year, with sandy grit that follows you everywhere. The plants are all prickly, and then there are the critters that choose to live there. As daunting as their home, Fort Huachuca has the aforementioned spiders and snakes, as well as an assortment of creatures like lizards, scorpions, ants, wasps, and other things that all look like they want to bite you.
Even the robotic hawks, erected around the compound to screech with annoying regulatory in a mostly vain effort to scare off pigeons, can get on your nerves during those times when you have to be outside under a searing sun.
Exacting and Rigorous
The DoD could have put their TIC in Hawaii, but that would not make for a fitting metaphor. And because the TIC is in Fort Huachuca, that is where the ScienceLogic team has to go to from time-to-time to endure the exacting and rigorous testing that is required for SL1 to be listed among the systems on the DoDIN APL. And it is well worth the time and effort.
The second blog of this four-part series described the DoDIN APL and why it matters to the federal government. It is a long and arduous process, and just the start of an ongoing journey. Getting certified for the APL is the first of three steps mandated by the Federal Information Security Modernization Act (FISMA). Under the Unified Capabilities Framework (UFC) technology lifecycle, all approved vendors must accredit and maintain their systems to DoDIN standards.
ScienceLogic Is Up to the Task
The goal is to ensure that all hardware, software, applications, and services comprising the DoD’s extensive IT infrastructure are hardened to endure the cyber threats faced by that agency.
That infrastructure supports 2.9 million users across 4,800 locations in 160 countries and is bombarded by more than 13 million attacks every day. There can be no weak links in the security chain, and as the first AIOps platform approved for the DoDIN APL, ScienceLogic is determined to make sure our SL1 platform is up to the task.
Achieving DoDIN APL certification requires a twelve-step processes:
- Confirm Sponsorship – Vendor must obtain government sponsorship (primary and secondary) to ensure adequate coverage in meetings and communications throughout the process.
- Submit Initial Documentation – Vendor submits product(s) for testing via the APL Integrated Tracking System (APLITS) with accompanying system, product, and company documentation.
- Receive TN – Vendor receives unique certification number (TN). TNs are grouped under a “device type,” or category of products.
- Attend ICM – Vendor attends an initial contact meeting (ICM) to determine overall readiness to proceed with testing.
- Submit SAR – Vendor submits self-assessment report (SAR) of cybersecurity (CS) requirements (open, closed, not applicable).
- Compensate Government – Vendor compensates government either by equipment left at the facility or a fee.
- Perform Tests – Vendor and government perform CS and interoperability (IO) tests.
- Receive and Respond to Draft CAR and TDR – Vendor receives, then responds to, draft test output—Cybersecurity Assessment Report (CAR) and Test Discrepancy Report (TDR)—created by the testing action officer (CS) and Joint Interoperability Test Command (IO) respectively.
- Submit Draft MUDG – Vendor creates and submits draft Military Unique Deployment Guide (MUDG) which defines additional steps to lock-down or harden a system beyond a typical installation and configuration.
- Attend Out-Briefs – Vendor attends out-briefs to review the status of findings and confirm timing to fix if necessary.
- Complete Out-Brief Actions – Vendor completes any outstanding items from the out-brief.
- Get Posted on DoDIN APL – Vendor gets posted on DoDIN APL… and celebrates!
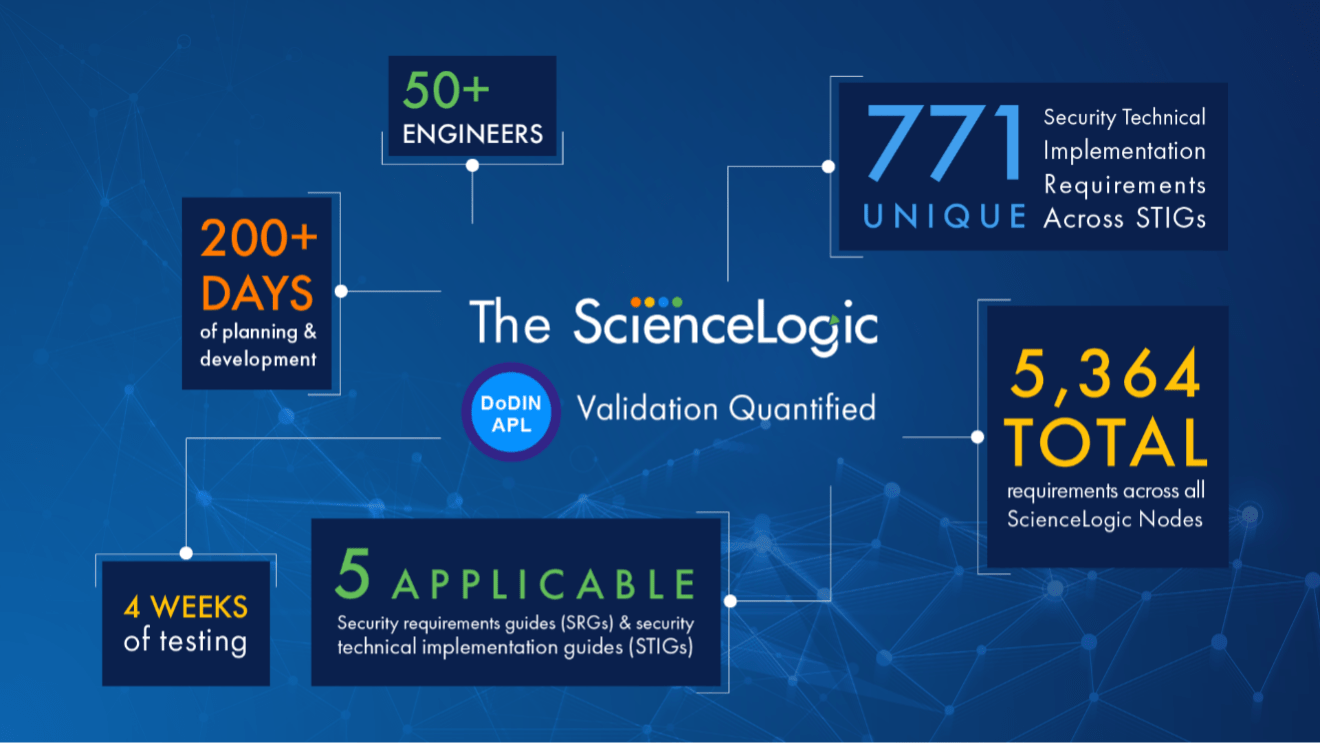
If those steps look daunting, it’s because they are. Here’s more statistics involved in completing the process.
Worth Every Step of the Journey
Why do we do it? Because it’s worth every step of the journey. ScienceLogic recognizes the importance of operating our nation’s critical military information systems at the highest possible levels of security. And we know that, by meeting the stringent requirements of the DoD, our customers in every industry can have equal confidence that we have engineered a product that will function as a secure part of a secure technology infrastructure.
I don’t like spiders and snakes, but if that’s what it takes to demonstrate to the Department of Defense—and to your enterprise—that SL1 has what it takes to perform at the highest levels of security and interoperability, we’ll go through it all again. And we will, because we will not be complacent when it comes to delivering the best possible product to all our customers.
Learn more about ScienceLogic’s security posture >
 See ScienceLogic in actionTake a Tour
See ScienceLogic in actionTake a Tour Take Skylar One for a SpinStart Your Test Drive
Take Skylar One for a SpinStart Your Test Drive The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report
The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report
The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report Become a PowerPack PicassoRegister Today
Become a PowerPack PicassoRegister Today