A Legacy of Commitment and Trust
ScienceLogic has a long history of employing security best practices to deliver solutions that our customers can trust. Cyber-attacks are rising in frequency, sophistication, and the extent of damage they can inflict upon an organization’s operations, reputation, or worse, their customers. Therefore, ScienceLogic continues to maintain security vigilance and regularly evaluates vulnerabilities to ensure a robust security posture. Explore our multi-pronged approach to securing our solutions including customer data, and earning their trust.
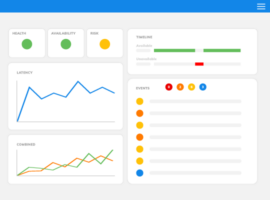
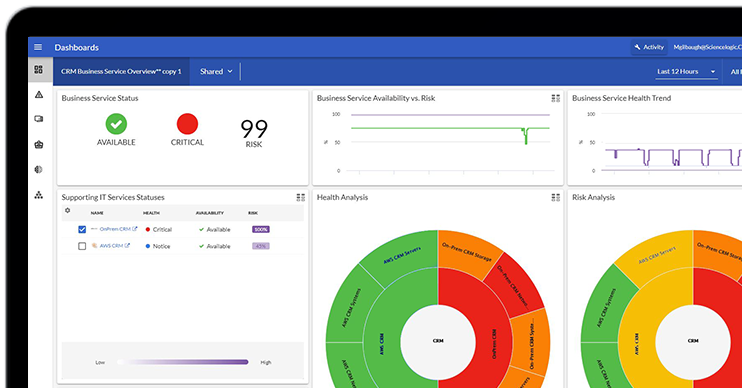
Product Security Features
Deployment
Deployment options: Choose your preferred deployment option: ScienceLogic-Managed SaaS, Customer-Managed On-Premises or Public Cloud. As your environment grows in scale, additional collectors can be deployed to cover additional infrastructure or geographic regions. Everything is centrally managed and accessed through a single web interface.
Government-specific deployments:
To meet U.S. Department of Defense (DoD) specifications, there is an option to install as a Military Unique Deployment (MUD) to comply with DoDIN APL (DoD Information Network Approved Products List) requirements.
ScienceLogic Government Cloud has FedRAMP Moderate Authorization and is available via the FedRAMP Marketplace.
Authentication
Secure user login: Customers can continue to adhere to their corporate policies via several authentication mechanisms such as configurable password requirements, SSO, Client Certificate & CAC Authentication. Skylar One (formerly SL1) supports enterprise-grade single sign-on (SSO) integration options for SAML and Active Directory/LDAP, as well as local authentication using email address and a password. User logins can be secured by multi-factor authentication.
Authorization
Flexible access & permission management: Skylar One allows customers to manage granular, role-based access for users and groups locally or via Active Directory, LDAP, SAML, CAC, PIV and multiple Identity Providers (IdPs) simultaneously.
Auditing
Audit logs: View an audit trail of actions performed by users in the platform, including user logins and logouts.
Monitor for illicit behavior: Setup alerts and events for monitoring unwanted behavior such as illicit processes, changes in performance, domain records, open ports, etc.
Data Security
Data Segregation
Dedicated instances: Skylar One SaaS customers are deployed in their own dedicated instance of Skylar One in ScienceLogic’s public cloud environment, inherently ensuring data segregation between customers.
Multi-Tenancy
Data access by ‘Organizations’: Skylar One’s built-in multi-tenancy allows customers to organize data by ‘Organizations’ within the same instance of Skylar One. This adds another layer of logical separation of customer data and better role-based access control by department, region, line of business, etc.
Incident Response Management
Continuous vigilance: Performance, availability, and security events are constantly monitored, and alerts are sent to a dedicated incident response team. Report security incidents here.
Highly Secure Data Centers
Secure data handling: Skylar One SaaS is deployed in AWS, which runs in ISO 27001 certified data centers. Skylar One follows industry standards for encrypting data. Data collection and transmission from Skylar One Agents, Skylar One Collectors, or via platform integrations is secured with white-listing, SSH tunnels, PhoneHome methods (to limit firewall configuration changes), and ‘Least Privileged’ access to each customer environment. Stored data is protected with AES encryption. Data in transit is protected via Transport Layer Security (TLS). Customers who use CrowdStrike can install CrowdStrike Agents on ScienceLogic Skylar One collectors for extended endpoint protection of Skylar One devices on customer networks.
High-Availability Architecture
Resiliency & redundancy: The microservices-based Skylar One SaaS platform is designed to be highly redundant when deployed. The Skylar One SaaS platform and its components (Compute, Storage, and Database nodes) are deployed in a highly redundant configuration across a cluster of data centers. The failure of one component automatically redirects traffic to a replica of the node instance within the redundant cluster, minimizing impact to the Skylar One SaaS platform availability.
Software Supply Chain Security
Threat Modeling
Security design considerations: Security starts in the requirements and design phase. That’s where our security architects help analyze potential attack vectors using threat modelling techniques before the actual implementation starts.
Secure Software Development Lifecycle Practices
Secure SDL: ScienceLogic enforces security best practices throughout the software development lifecycle such as OWASP 10 and peer code reviews. These best practices include:
- Automatically scanning for vulnerabilities and malware.
- Automatically running thousands of automated tests.
- Automatically signing assets and verifying signatures during installation.
- Conducting manual penetration testing.
- Ensuring all artifacts are transferred and stored encrypted.
- Tracking changes via a change management process.
Access to source code repositories is limited on both the network and the user level. Only authorized users can access code repositories and make changes to source code. Source code management systems are only accessible from within the ScienceLogic corporate network. Remote access to the ScienceLogic corporate network requires multi-factor authentication (MFA). Contact us to learn more.
Software Upgrades
Secure distribution: ScienceLogic implements several security controls and uses industry best practices to protect ScienceLogic software components like Skylar One, Skylar One Agent and Collectors, and Skylar One PowerPacks from malicious manipulation by attackers on the way to our customers’ infrastructure.
All steps are fully automated, from source code being compiled to binaries, to the upload of the binaries to the AWS infrastructure where they are available for customers to download. No manual, error-prone steps are involved. Data in transit is encrypted using industry standards (TLS 1.2). Every storage location involving data at rest is encrypted as well.
All installation packages are scanned for malicious software and digitally signed before they’re uploaded to AWS. The signatures are automatically verified during the update process on the customer infrastructure. If a verification fails (for example, due to installation package manipulation by an attacker), the update process is stopped. Learn more about our security features.
Internal & External Penetration Testing
Internal and third-party tests: On an ongoing basis, we test new and existing features. Our internal penetration tests are led by a certified penetration tester in our Security team. Our external penetration tests are performed bi-annually by independent security firms.
Vulnerability Scanning
On-going scanning: Vulnerability scanning is performed regularly using static code analysis, dynamic runtime scans, network scans, and third-party component scans.
Corporate Security
Vendor Management
Onboarding & ongoing checks: External vendor products that are leveraged within the Skylar One platform, or leveraged for delivery of the platform are subjected to a detailed security assessment to guard against various attacks such as attempts to inject malicious code, hijack internal processes etc.
Vendors are evaluated prior to onboarding and on a periodic basis or whenever there’s a significant change in their cyber risk rating.
All third-party libraries are evaluated for quality, performance, licensing, and vulnerabilities and require approval before being used.
Employee Awareness & Background Checks
Training & awareness: ScienceLogic conducts annual employee and contractor security training with quarterly boosters and spot-training as needed. Training topics include Ransomware, Social Media, Credential Management, Impersonation Attack, Data Handling, Fraud, Phishing, Identity Theft, etc. Additionally, employees participate in role-specific security training.
Secure access: Remote employees are required to log in using secure VPN with MFA.
Background checks: New employees are put through rigorous background checks.
Privacy
Customer data: Our privacy policy reflects our commitment to protecting personal data. To accommodate various privacy regulations such as General Data Protection Regulation (GDPR) or California Consumer Privacy Act (CCPA), Skylar One collects a very limited amount of PII about users (full name, work email address, work phone number), and only what is required for authentication and user management. The specific requirements of the customer’s organization regarding PII should be reviewed with the ScienceLogic delivery team to ensure the deployment meets the customer organization’s security requirements. Read our Privacy Policy to learn more about the type of personal information we collect, how we store it, how we use it, and what rights individuals have and how they exercise them.
Experience the difference.
Trusted by You, Attested by Industry Experts
ScienceLogic understands that taking a holistic approach to securing every possible touch-point for customers’ data—from corporate and physical security, development best practices, securing the supply chain, to securing how data is transmitted to and stored within our environment—are key to earning your trust. As stewards of that data, we leverage industry-standard security, privacy, and compliance frameworks with supporting materials that attest to our capabilities. So you can rest assured of a secure supply chain for your customers.

DoDIN APL
ScienceLogic is named on the U.S. Department of Defense Information Network Approved Products List (DoDIN APL). As the first complete end-to-end IT infrastructure monitoring solution ever to conform to the DoD’s rigorous security and interoperability standards, government agencies can now purchase and implement ScienceLogic’s IT infrastructure monitoring products on an expedited basis, and dramatically mitigate their network management challenges. As part of being listed on the APL, ScienceLogic complies with the requirement for timely patching of issues to maintain the operational availability, confidentiality, and integrity of customers’ systems.

FedRAMP
ScienceLogic has achieved FedRAMP® Moderate Authorization. The ScienceLogic Government Cloud is available in the FedRAMP Marketplace. FedRAMP Moderate certification ensures that ScienceLogic meets stringent federal security requirements, making it a trusted choice for handling sensitive government data in the Cloud.

FIPS 140-2 Compliant Cryptography
Products that collect, store, transfer, share, and disseminate sensitive but unclassified (SBU) information must be certified for use in U.S. government departments (such as Department of Defense). A customer’s Skylar One configuration can be made FIPS 140-2 compliant. Specific requirements for FIPS 140-2 compliance should be reviewed between the customer and the ScienceLogic delivery team to ensure the deployment meets each customer organization’s security requirement.

CSA Star Level Two
ScienceLogic is registered in the Cloud Security Alliance’s (CSA) Security, Trust and Assurance Registry. CSA provides a comprehensive framework for cloud provider trust and assurance, which is designed to recognize the varying assurance requirements and maturity levels of providers.
ScienceLogic completed the security and privacy independent assessments and verification based off the CSA’s Cloud Controls Matrix required for CSA Star Level Two. For more details, you can review the CSA listing at: Cloud Security Alliance – ScienceLogic CSA Level Two

ISO 27001
Skylar One SaaS is deployed in AWS which runs in ISO 27001 certified data centers.
SOC 2 Type II
ScienceLogic’s On-Premises and SaaS deployment offerings are evaluated on an annual basis by a third party in a SOC 2 Type II examination. The product and service are evaluated against controls related to Security, Availability, Processing Integrity, and Confidentiality. A copy of this report may be shared with third parties once a non-disclosure agreement is in place. Request SOC 2 Type II Report

Data Residency
We offer customers the ability to meet data residency requirements in multiple jurisdictions. Please see the SaaS Operations section to learn more about global availability of Skylar One SaaS or contact us for more details.

Privacy Policy
ScienceLogic’s privacy policy reflects our commitment to protecting personal data. To accommodate various privacy regulations such as GDPR or CCPA, Skylar One collects a very limited amount of PII about users (full name, work email address, work phone number), and only what is required for authentication and user management. The specific requirements of each customer’s organization regarding PII should be reviewed with the ScienceLogic delivery team to ensure the deployment meets each customer organization’s security requirements. Read our Privacy Policy to learn more about the type of personal information we collect, how we store it, how we use it, and what rights individuals have and how they exercise them.

HIPAA
An Skylar One Collector or Skylar One Agent can be installed in environments where customers have certain security or regulatory restrictions, including with respect to the Health Insurance Portability and Accountability Act (HIPAA). By default, Skylar One does not collect regulated information such as protected patient information or data subject to export restrictions. Customers should review their security requirements with the ScienceLogic delivery team.

PCI/DSS
An Skylar One Collector or Skylar One Agent can be installed in environments where customers have certain security or regulatory restrictions, including with respect to Payment Card Industry Data Security Standards (PCI/DSS). ScienceLogic does not by default collect any cardholder data. In addition, the Skylar One Collectors and Skylar One Agents can be configured to satisfy PCI/DSS compliance requirements. By default, Skylar One does not collect regulated information such as payment cardholder data or data subject to export restrictions. Customers should review their security requirements with the ScienceLogic delivery team.

Accessibility and WCAG/508
ScienceLogic is committed to constantly improving the accessibility of our Skylar One Platform and associated products to serve a wide variety of customers with varying accessibility needs. Our team of designers and developers implement best practices in accessible design and inclusive user experience.
With each major release, we generate Accessibility Conformance Reports (completed VPATs) to document our products’ conformance with accessibility standards outlined in the W3C’s Web Content Accessibility Guidelines (WCAG), as well as Section 508 of the US Rehabilitation Act and Europe’s EN 301 549, important standards requiring electronic and information technology be accessible to people with disabilities.
Skylar One SaaS – Manage Your Core Business With Confidence
With Skylar One SaaS, your Skylar One instance is hosted, managed, and updated by ScienceLogic in public cloud – so your team can focus on unlocking the true value of Skylar One to grow your core business. Customers can install Skylar One Collectors and Agents to collect relevant and permitted data points around performance, configuration, availability etc. from any combination of on-premises and cloud customer environments.

Resilient Architecture
- Microservices-based Skylar One SaaS application and its components (Compute, Storage and Database nodes) deployed in a highly redundant configuration across a cluster of data centers within the same geographic region ensuring high-availability
- Daily data backups to ensure swift failover and recovery
- Scale up or down to meet customer needs with no impact to Skylar One performance
Submit a Request
Evaluating ScienceLogic for your IT modernization and automation needs? Need to check-off your vendor security requirements? We’ve got the information you need. Click on the links below to request access to the following reports.