When Static Metrics Cannot Model Dynamic Risk
For years, infrastructure stability could be approximated through static limits. If CPU utilization exceeded a defined percentage or response time crossed a fixed boundary, risk was assumed to increase in a predictable way. Monitoring systems were designed around that assumption, and for contained environments, it largely held true.
During conversations at Nexus Live 2025, ScienceLogic’s annual customer conference, leaders across industries acknowledged that this assumption no longer reflects how modern systems behave. Distributed architectures have changed the nature of degradation. What once presented as a clear breach now accumulates through interaction across services.
The Assumption Behind Static Thresholds
Traditional monitoring models treated infrastructure components as largely independent. A server metric indicated server health. A database alert reflected database strain. A threshold breach signaled localized risk.
Hybrid and cloud-native systems weaken that independence. Services are composed of interlocking dependencies across on-premises environments, public clouds, APIs, shared services, and third-party integrations. Scaling is elastic. Routing is dynamic. Load distribution shifts based on demand and orchestration logic. In such environments, degradation rarely originates from a single point. It emerges gradually through interaction across the broader ecosystem.
Nonlinear Degradation in Distributed Architectures
Leaders described instability not as a dramatic event but as an erosion of margin. A slight increase in latency within an authentication service may remain within tolerance. A concurrent increase in database response time may not exceed its threshold. A shared messaging layer may operate closer to saturation than usual without triggering alarms. Individually, each condition appears acceptable, yet collectively they increase fragility.
Static thresholds evaluate metrics in isolation. They do not account for amplification effects across dependency chains. Under load shifts or traffic surges, minor degradations can compound, accelerating impact before any single metric signals urgency. The result is a structural gap between visible health and actual exposure.
Correlation Without Context
Many organizations have introduced correlation engines to cluster alerts and reduce noise. This improves signal clarity but does not inherently resolve the underlying limitation. Correlation can group related events, yet without continuously reconciled service topology and business weighting, prioritization remains infrastructure-centric.
In distributed systems, risk is defined less by the loudest metric and more by where that metric sits within the service graph. An alert tied to a revenue-generating service carries different weight than an isolated infrastructure anomaly. Without modeling these relationships dynamically, teams may respond efficiently while still missing accumulating exposure elsewhere.
When SLA Commitments Depend on Interaction
Service level agreements are defined by user experience and contractual obligation rather than discrete infrastructure states. In threshold-centric models, response is triggered once a visible breach occurs. In distributed environments, waiting for that breach often compresses remediation windows and increases commercial risk.
The leaders we spoke with consistently emphasized a shift toward proactive detection. They are expected to identify instability before customers or stakeholders are affected. Meeting that expectation requires evaluating how interacting signals alter service stability, not simply whether a metric has crossed a predefined limit.
From Static Limits to Dynamic Modeling
Protecting distributed systems requires moving beyond isolated metric evaluation toward service-centric modeling. This approach continuously reconciles telemetry with dependency mapping, evaluates how multiple signals interact, and assesses exposure in relation to business commitments. Thresholds remain useful for identifying acute deviations, but they are insufficient as primary control mechanisms in dynamic architectures.
As distributed environments become more dynamic, organizations need observability strategies that connect infrastructure signals to service impact. For IT leaders operating complex hybrid environments, the challenge is no longer just collecting more telemetry. The real priority is turning that telemetry into actionable insight that reflects how services actually behave in production. That shift is essential to improving resilience, protecting digital experiences, and operating with greater confidence.
Confidence in distributed systems does not come from watching individual gauges. It comes from understanding how the system behaves as an interconnected whole.
 See ScienceLogic in actionTake a Tour
See ScienceLogic in actionTake a Tour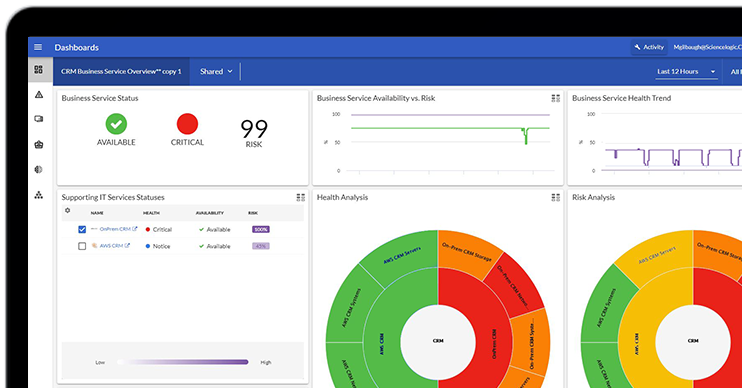 Take Skylar One for a SpinStart Your Test Drive
Take Skylar One for a SpinStart Your Test Drive The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report
The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report
The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report Become a PowerPack PicassoRegister Today
Become a PowerPack PicassoRegister Today
