Accountability in the Age of Distributed Systems
When Reliability Becomes Responsibility
The leaders responsible for modern IT environments rarely talk about features first. They talk about responsibility.
In conversations at Nexus Live 2025, ScienceLogic’s annual customer conference, executives and architects across healthcare, federal systems, managed services, telecom, and enterprise IT described modernization not as a tooling upgrade, but as an escalation of accountability.
As digital services become the primary interface between organizations and the people they serve, reliability stops being technical hygiene and becomes a promise. When something fails, the impact is no longer contained within infrastructure teams. It reaches patients, customers, citizens, and revenue streams. It reaches executive leadership. It reaches trust.
That shift reframes the purpose of observability and automation. The question is no longer whether teams can see their environments. The question is whether their architecture is designed to protect what has been promised.
Responsibility Before Technology
Across industries, leaders emphasized that their primary concern is not data volume or dashboard density. It is clarity under pressure. They need to understand which services are exposed, which dependencies are vulnerable, and which commitments are at risk at any given moment.
In healthcare environments, instability affects patient care. In federal systems, performance degradation can influence mission readiness. In managed services, customers expect providers to identify and resolve issues before those issues become visible to end users. The common thread is not infrastructure. It is obligation.
In this framing, observability becomes less about measurement and more about preservation. Automation becomes less about speed and more about reducing the probability that human fatigue or fragmented tooling will allow small issues to compound into larger failures.
Complexity Changes the Risk Equation
Hybrid and multi-cloud architectures have stretched the fabric of IT environments in ways that are not always visible from a dashboard. Workloads shift dynamically. Dependencies span providers. Shared services create indirect coupling between systems that appear independent on the surface.
In these environments, risk rarely announces itself through a single catastrophic event. It accumulates. A modest increase in latency in one service may remain within tolerance. A minor configuration drift in another may not trigger an alert. A shared dependency may operate closer to capacity than expected without breaching defined thresholds.
Individually, each condition appears manageable. Together, they narrow the margin for error.
Several leaders described this state as a persistent background tension. The system may appear stable, yet confidence depends on whether the architecture can anticipate how interacting signals affect service commitments before degradation becomes disruption.
Visibility Does Not Eliminate Strain
Most organizations have achieved broad telemetry coverage. Metrics, logs, traces, and events stream continuously into centralized platforms. Real-time dashboards provide visual assurance that systems are operating within defined limits.
Yet visibility alone does not remove strain. In some cases, it increases cognitive load. High volumes of alerts require interpretation. Disconnected tools require translation. Engineers reconstruct service relationships under time pressure, correlating signals across multiple systems to determine actual impact.
Visible stability can mask underlying tension. The dashboards may not indicate disruption, yet engineers continue testing assumptions, tracing service relationships, and evaluating whether the system’s margin for error is narrowing.
From Monitoring to Assurance
The organizations that expressed greater confidence were not necessarily those with the most data. They were those with the most coherent control frameworks. Telemetry was aligned with continuously updated service topology. Events were enriched with context before triage began. Automation operated within clearly defined policy boundaries, reducing repetitive manual effort and standardizing response.
In some environments, onboarding and remediation workflows that once required days were reduced to minutes. In others, correlated insight enabled proactive intervention before customers were aware of instability. These improvements were described not as technical achievements but as structural relief. The system itself absorbed part of the burden that previously rested entirely on people.
This distinction matters. When architecture carries responsibility alongside the teams accountable for outcomes, confidence grows. When architecture simply reports state, strain persists.
Modern IT environments will continue to expand in complexity. Digital services will remain tightly coupled to revenue, mission, and customer trust. Responsibility will not diminish. The question facing technology leaders is whether their observability and automation frameworks merely describe conditions or actively protect commitments.
The leaders we spoke with were not asking for more dashboards. They were asking for systems designed to share the weight—platforms capable of unifying visibility while actively protecting service commitments.
 See ScienceLogic in actionTake a Tour
See ScienceLogic in actionTake a Tour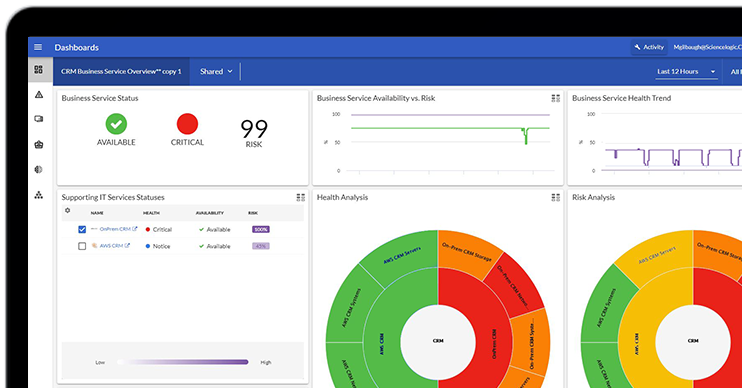 Take Skylar One for a SpinStart Your Test Drive
Take Skylar One for a SpinStart Your Test Drive The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report
The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report
The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report What's New for Business ServicesRegister Today
What's New for Business ServicesRegister Today
