Why Visibility Must Evolve Into Context
If distributed architectures have altered how systems degrade, then the way organizations model operational must evolve accordingly. Threshold monitoring evaluates individual metrics. Correlation clusters related alerts. Neither, on its own, explains how instability in one component alters exposure across an interconnected service landscape.
In conversations at Nexus Live 2025, ScienceLogic’s annual customer conference, leaders described this distinction with clarity. Many had already consolidated tools and improved signal reduction. Alert volume was lower. Dashboards were cleaner. Yet confidence remained uneven. The missing element was not more data. It was context.
Correlation Reduces Noise. Context Reduces Risk.
Correlation engines group related events and suppress duplicates. This improves triage efficiency and reduces cognitive overload. However, correlation operates primarily at the signal layer. It identifies patterns in telemetry, but it does not always show operational or business consequences.
Service-centric observability shifts the unit of analysis. Instead of evaluating infrastructure components in isolation, it models the relationships between infrastructure, applications, dependencies, and the services those components collectively support. A latency spike in a shared authentication service does not carry uniform impact. Its significance depends on which revenue-generating or mission-critical services rely on it at that moment.
Without continuously reconciled service topology, prioritization becomes reactive to signal intensity rather than exposure magnitude. The loudest alert is not always the most consequential. That is where service-centric observability creates a meaningful advantage.
From Component Health to Relationship Modeling
Distributed environments introduce indirect coupling across services that static monitoring cannot fully capture. A containerized workload scaling event may shift traffic patterns across regions. An API dependency may introduce performance variability that propagates across downstream services. Shared infrastructure layers can create systemic fragility that does not manifest as a single, obvious breach.
Service-centric observability treats the environment as a living graph rather than a collection of independent nodes. Telemetry is interpreted within the context of dependency chains. Changes in one domain are evaluated for their impact on adjacent services. Risk is modeled dynamically rather than inferred from isolated thresholds.
This approach alters prioritization logic. Instead of responding to metrics based solely on deviation from normal ranges, teams evaluate how those deviations influence service commitments. The focus moves from “Is this metric out of bounds?” to “What does this mean for service health, customer experience, and what is the business impact?”
Business Weighting and SLA Alignment
Leaders consistently emphasized that not all services carry equal consequence. An internal development tool and a customer-facing payment system cannot be treated with the same urgency. Yet infrastructure-centric monitoring often surfaces alerts without embedded business weighting.
Service-centric observability incorporates business context directly into triage decisions. Dependencies are mapped to the services they support, and those services are weighted according to revenue impact, regulatory exposure, or mission criticality. When instability emerges, its priority is determined by consequence, not merely by severity.
This alignment transforms SLA protection from a reactive response to a modeled safeguard. Exposure is evaluated in terms of service commitments rather than infrastructure deviation alone.
The Control Layer Between Insight and Action
As organizations introduce greater levels of automation and AI-driven assistance, the integrity of this context layer becomes increasingly important. Automation accelerates execution. AI accelerates prioritization. Without service-aware modeling, both can amplify misaligned decisions.
Service-centric observability functions as the control layer between insight and action. It ensures that decisions, whether human or automated, are grounded in an accurate representation of service relationships and business impact. It distributes responsibility across architecture rather than concentrating it solely on individuals interpreting dashboards under pressure.
In distributed systems, confidence does not come from reducing alerts alone. It comes from knowing that the system understands how its parts interact and how those interactions influence commitments.
When context becomes continuous and dynamic, teams move beyond reacting to signals. They begin managing exposure deliberately. That shift lays the foundation for governed automation and measurable SLA protection. Observability becomes more than a way to detect issues. It becomes a way to protect service outcomes, strengthen operational resilience, and give IT leaders greater confidence in every decision they make.
That is the real value of service-centric observability: not just more visibility, but clearer priorities, better decisions, and stronger alignment between technology performance and business impact.
 See ScienceLogic in actionTake a Tour
See ScienceLogic in actionTake a Tour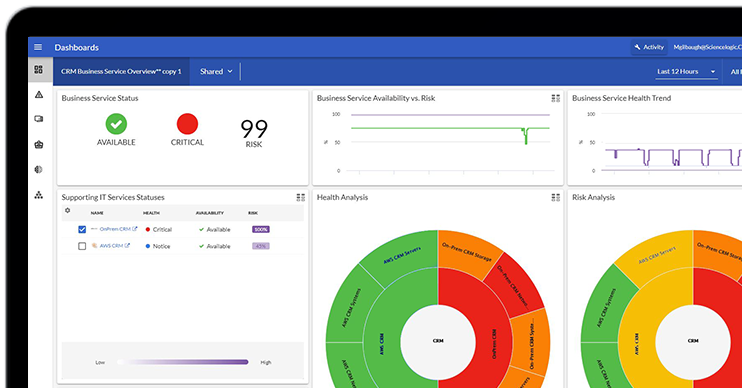 Take Skylar One for a SpinStart Your Test Drive
Take Skylar One for a SpinStart Your Test Drive The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report
The Gartner® Magic Quadrant™ for Observability PlatformsRead the Report The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report
The Forrester Wave™: AIOps Platforms, Q2 2025Access the Report What's New for Business ServicesRegister Today
What's New for Business ServicesRegister Today
