Read this eBook to learn how service providers can avoid the costs and risks of non-compliance.
The barriers to entry in the service provider industry have come down—causing the MSP market to grow by nearly 33% last year and reaching nearly $355 billion by 2026. That means competition is increasing along with the market’s growth. To differentiate in a market that demands high performance in areas addressing risk, compliance, and availability, here are five areas to focus on.
1. Domain Expertise
Organizations that handle regulated data and contract with an MSP rely on the say-so of that MSP for any assurances that their operations do not violate applicable laws. Maintaining domain expertise in the regulations that apply to your operation is essential, and there are plenty of laws and standards that exist such as GDPR, HIPAA, PCI-DSS, SOX, ECA, and GLBA.
2. Specialization
Because of the many and changing data security and management regulations, it can be difficult for all but the largest MSPs to address the needs of the broader well. That’s why MSPs should consider specializing in a particular industry or geo—where the scope of compliance is narrower.
3. Standards and Certification
For an MSP to differentiate in a crowded, confusing market where certifications for vital security and regulatory practices are not currently required means self-certifying by establishing and documenting the highest operational standards based on recognized best practices.
4. Documentation
Without documentation, there is no compliance. That is why, building from a baseline for security practices, supporting IT operations through documentation for processes like change management, policy enforcement, and other operations is vital to security and compliance.
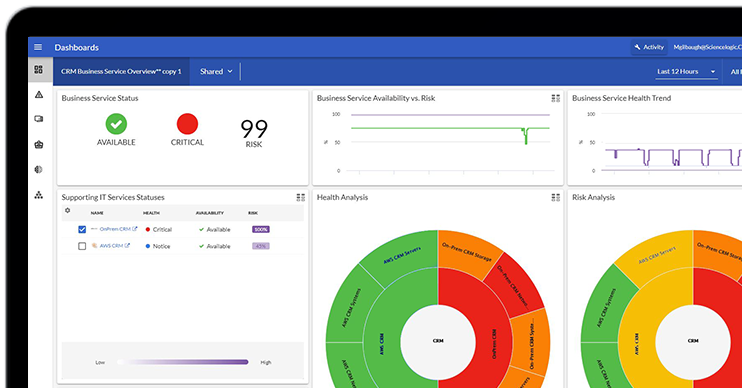
5. State-of-the-Art Tools
A state-of-the-art ITOps and risk compliance program requires state-of-the-art tools designed to capture and document operational data at the speed of operations. Investing in tools that can keep pace with the speed of data in today’s highly complex IT networks is not an option, but a requirement.